Impact¶
Overview
Quote
Is there any machine readable version of the "technical" impact of a vulnerability that is standardized and grouped?
For example:
- Allows for privilege escalation
- Allows for application data manipulation
- Allows to run shell code at the user level
Quote
No is the short answer AFAIK...
Tip
See BSidesDub talk Understanding and Using Impact so you know what Vulnerabilities to fix first and associated Slides
Technical Impact¶
Technical Impact is different than Attack Pattern!
“CWE is the root mistake, which can lead to a vulnerability (tracked by CVE in some cases when known), which can be exploited by an attacker (using techniques covered by CAPEC)”, which can lead to a Technical Impact (or consequence), which can result in a Business Impact
https://riskbasedprioritization.github.io/risk/Vulnerability_Landscape/#key-risk-factor-standards
Impact in CVE Schema¶
The CVE Schema contains a field for impacts and it uses the "CAPEC ID that best relates to this impact." and a "description" for "impact type information".
"impacts": {
"type": "array",
"description": "Collection of impacts of this vulnerability.",
"minItems": 1,
"uniqueItems": true,
"items": {
"type": "object",
"description": "This is impact type information (e.g. a text description.",
"required": ["descriptions"],
"properties": {
"capecId": {
"type": "string",
"description": "CAPEC ID that best relates to this impact.",
"minLength": 7,
"maxLength": 11,
"pattern": "^CAPEC-[1-9][0-9]{0,4}$"
},
"descriptions": {
"description": "Prose description of the impact scenario. At a minimum provide the description given by CAPEC.",
"$ref": "#/definitions/descriptions"
}
}
}
},
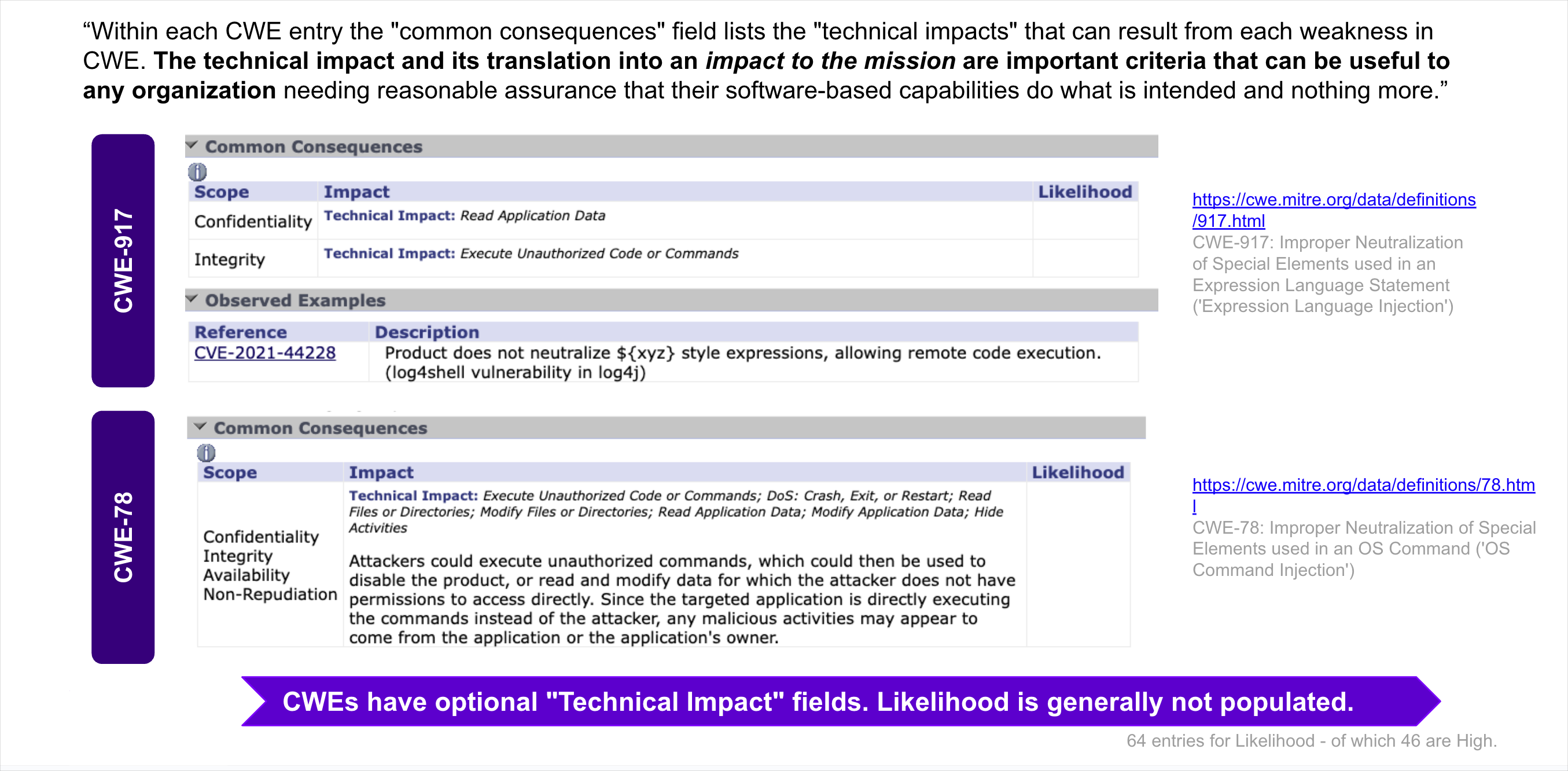
MITRE CWE Common Consequences¶
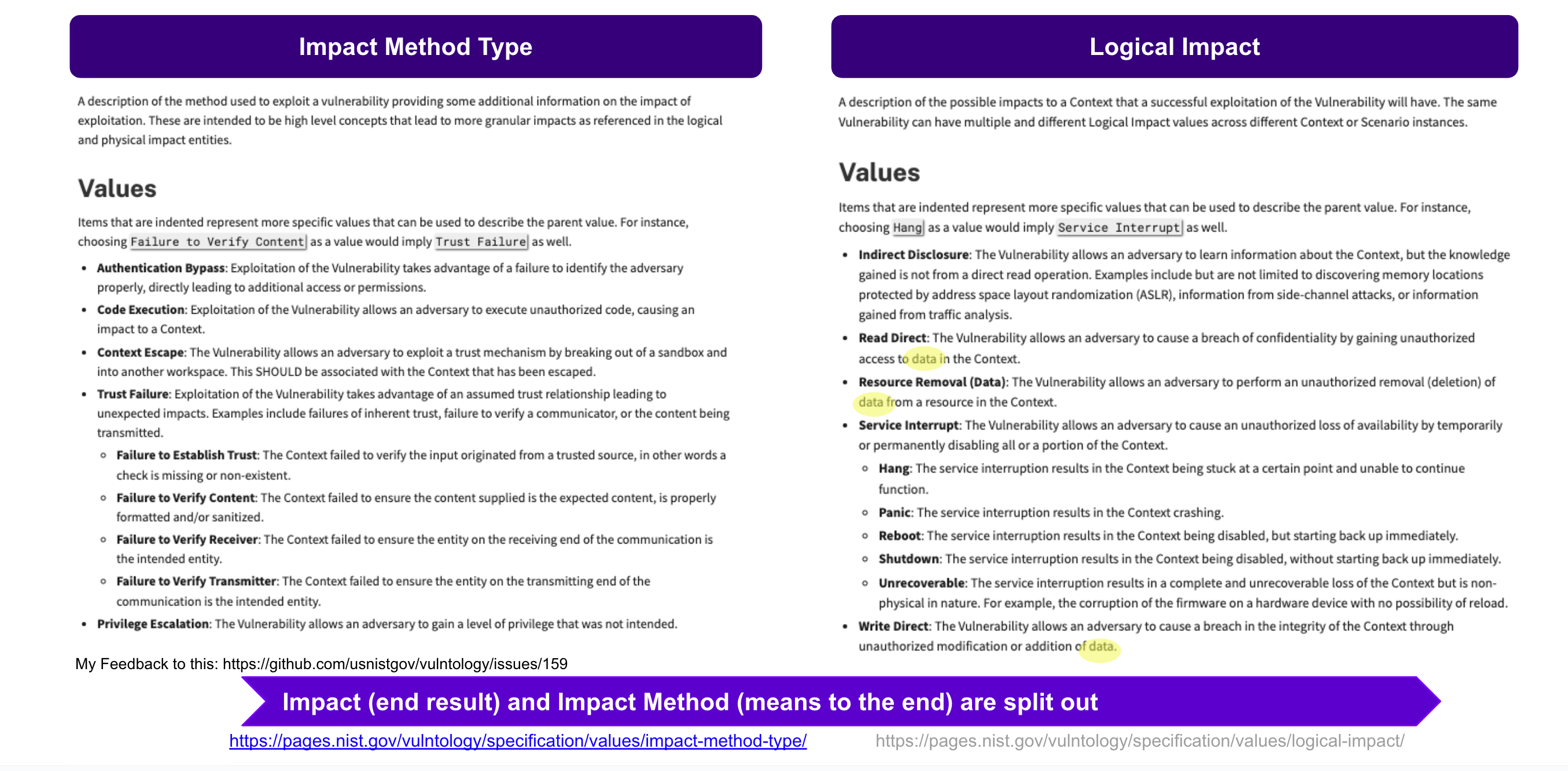
NIST Vulntology¶
NIST Vulntology defines:
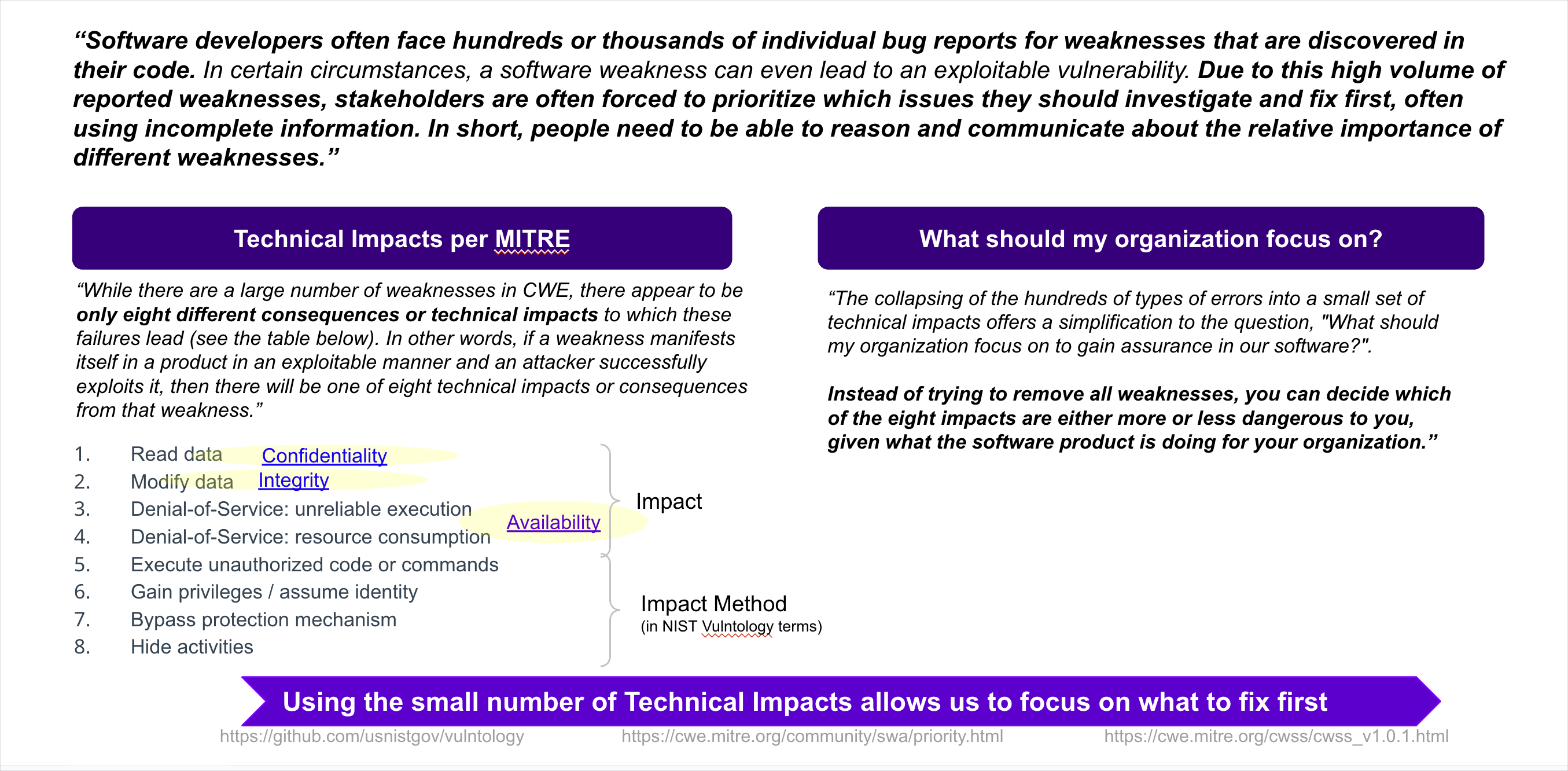
MITRE Technical Impacts¶
MITRE CAPEC (Common Attack Pattern Enumerations and Classifications) lists 8 Technical Impacts, in addition to the many CAPEC attack patterns.
- These can be mapped to NIST Vulntology Impact and Impact Method.
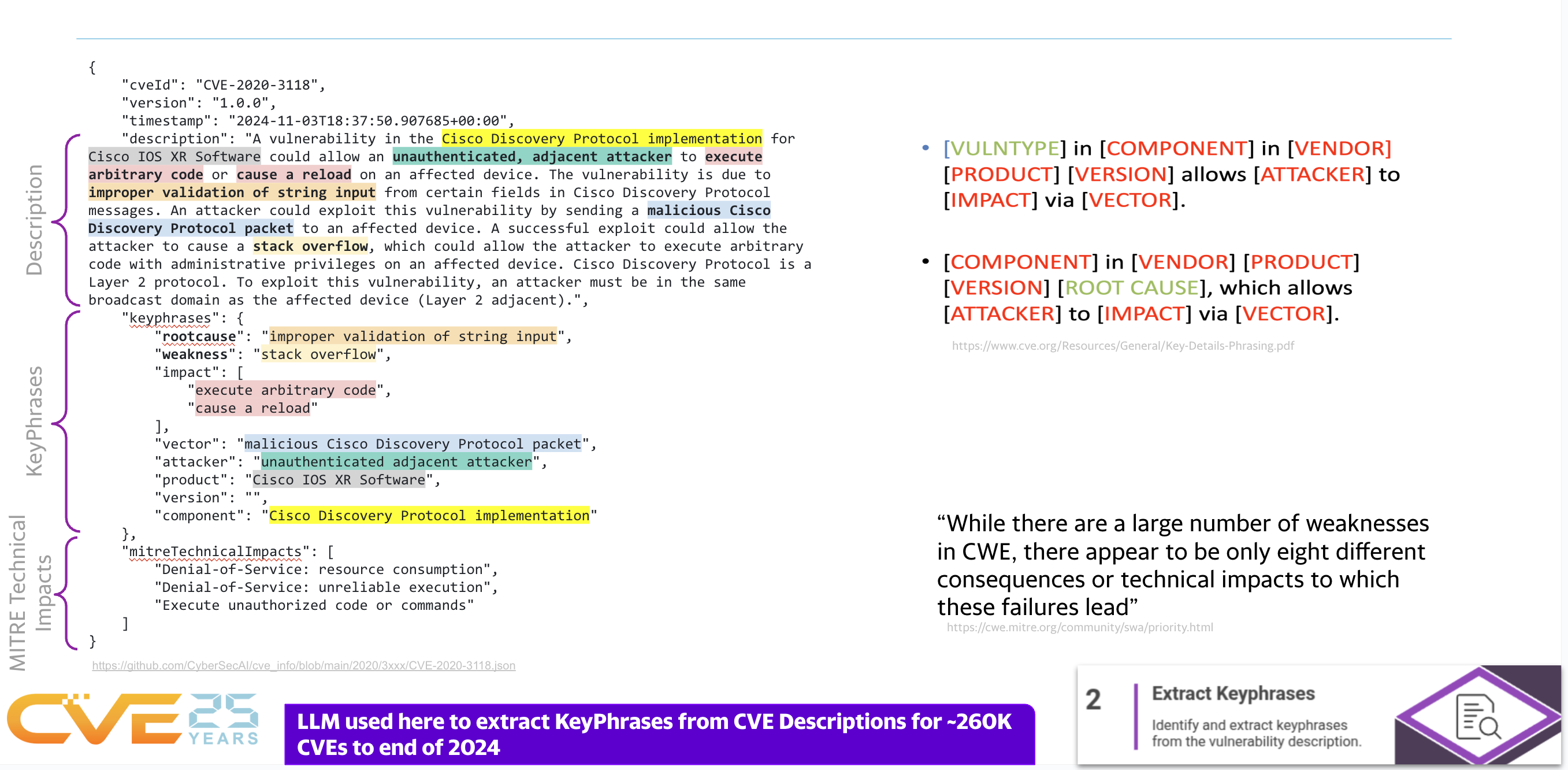
Impact Text and MITRE Technical Impact Extraction from a CVE¶
Per Vulnerability Root Cause Mapping with CWE: Challenges, Solutions, and Insights from Grounded LLM-based Analysis, FIRST Vulncon 2025, it is possible to
- extract the impact keyphrases from the CVE Info (Description and reference content)
- map the impacts to the MITRE Technical Impacts
Put the impact in the impact field 💡
💡 The impact keyphrases, and the MITRE Technical Impacts that they map to, could be placed in the CVE schema impacts field.
Takeaways
- The Technical impact is useful for end users (beyond the CVSS Confidentiality, Integrity, Availability impact) which is not so useful as it is not granular.
- Technical impact is not well represented in published CVEs today, even though there is an "impacts" field in the CVE schema.
- People may want to know the Impact more than the CAPEC (where CAPEC lives under Impact in the schema - and is often used as the only representation of Impact in a CVE, if at all)
- The CVE Description (and reference content) impact keyphrases, and the MITRE Technical Impacts that they map to, could be placed in the CVE schema impacts field.